This morning, we woke to a major announcement that Britain, the US, and EU have disrupted the Lockbit cybercriminal gang. We have all come to know the Lockbit group as one of the most sophisticated…
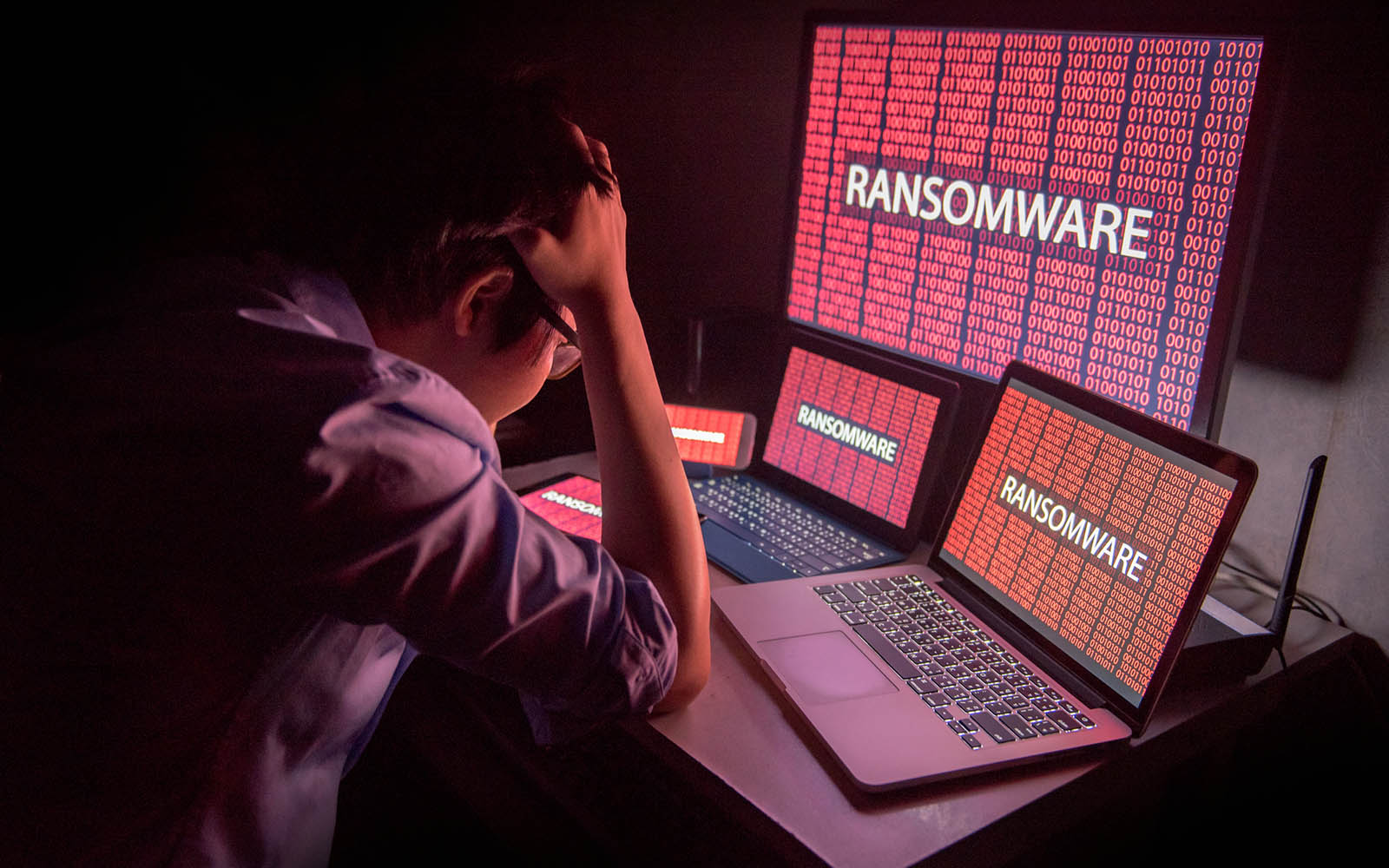
Anything goes in a war. According to technology and security experts, the ongoing battles with cybercriminals are escalating exponentially and are rapidly turning into “no holds barred” situations.…
The Top 8 Myths About Ransomware
With 24/7 news cycles and an overabundance of social media streams, the flow of information available on the internet is mind-boggling. Unfortunately, the accuracy of the reports, suggestions, and…
Why Ransomware Protection is the New IT Standard
Cybersecurity is big business today. For the criminal element, hacking and ransomware delivery high-return and relatively low effort activities and the significant rise in revenue is fueling…
The “worst-case” scenario is no longer unexpected in the channel. MSPs are increasingly on the receiving end of the cybersecurity attacks that they spend so much time and money trying to stop for…
The data and network protection market is hot. From the smallest firms to the largest enterprise organizations, businesses need quality cybersecurity support, and most can benefit from a range of…
IT security threats are more of a concern to the business community than ever before. Cybercriminals are attacking from multiple angles, from the standard email and social engineering schemes to…
Business is changing. Not only are the SMB clients you support transforming their operations from WFH and hybrid work environments to the adoption of more cloud services, but larger organizations are…
WFH is a Prime Environment for Ransomware Attacks
Employees need a safe working environment. Whether on a construction site or sitting in an office, employees need guidance and support to ensure they stay true to workplace procedures and best…