There is a new variant on the old ransomware theme that has been introduced into the wild. Jigsaw ransomware not only locks your computer to encrypt your files but it also deletes them if you don’t pay the ransom quickly enough. Although not as sophisticated as other versions of ransomware before it, Jigsaw ransomware demonstrates two things. Ransomware continues to evolve with new variants released at an alarming rate, and ransomware is so easy to buy and distribute that a 12-year-old could pull this off.
“Try anything funny and the computer has several safety measures to delete your files.” – Jigsaw Ransom
Jigsaw was named after the iconic character from the movie “Saw” and a photo of the character stares at you menacingly behind the ransom note. This gives the ransom note a “creepy” factor not seen since the Sony hack that included a skeleton in the background. The photo of Jigsaw is certainly meant to intimidate the victim and even worse; this latest ransomware version includes a timer that counts down from 60 minutes to increase the victim’s panic. Each hour that passes without a ransom payment results in deleted files. The first hour the ransomware deletes one file, but if you wait too long, the number of files deleted escalates quickly with each passing hour. After the initial infection, each time the computer is rebooted or the ransomware process is terminated, the ransomware will delete 1000 files from the victim’s computer. After 72 hours have passed without payment; Jigsaw deletes all remaining encrypted files.
Cerber: Ransomware Speaks Bitcoin Demand
CryptoJoker – Ransomware You Can Negotiate With
The Jigsaw Ransom
Your computer files have been encrypted. Your photos, videos, documents, etc....
But, don't worry! I have not deleted them, yet.
You have 24 hours to pay 150 USD in Bitcoins to get the decryption key.
Every hour files will be deleted. Increasing in amount every time.
After 72 hours all that are left will be deleted.
If you do not have bitcoins Google the website localbitcoins.
Purchase 150 American Dollars worth of Bitcoins or .4 BTC. The system will accept either one.
Send to the Bitcoins address specified.
Within two minutes of receiving your payment your computer will receive the decryption key and return to normal.
Try anything funny and the computer has several safety measures to delete your files.
As soon as the payment is received the crypted files will be returned to normal.
Thank you
How it Works

Once it is launched, Jigsaw scans the drives for a number of file extensions, encrypts these files using AES encryption, and then appends a .FUN, .KKK, .GWS or .BTC extension to the file name.
Jigsaw actually keeps track of the files it has encrypted in this file. %UserProfile%\AppData\Roaming\System32Work\EncryptedFileList.txt.
It also assigns a bitcoin address and saves that in %UserProfile%\AppData\Roaming\System32Work\Address.txt.
Next, Jigsaw creates a startup task that starts the ransomware each time you log in to Windows. As previously mentioned, each time the ransomware starts, it deletes 1000 of the files it has already encrypted. If the ransom is not paid within 60 minutes, Jigsaw will delete a certain number of files depending on how many times the counter has been reset. Each time the counter is reset, it will increase the file delete count which causes even more files to be deleted on the next reset. If a victim does pay the ransom, there is a button they can click to check on the payment. When the button is clicked, the ransomware checks http://btc.blockr.io/site to see if payment has been made to the assigned Bitcoin address. If the amount of Bitcoins in the assigned address is greater than the recorded payment amount; then the files will automatically be decrypted. Although most ransoms are in the amount of $150, we have found Jigsaw ransoms ranging from $20 to $200.
Gone Phishing: Why Human Resources is Vulnerable to Crypto Ransomware Attacks
How Many of Your Employees Will Get Phished Today?
Files Associated with Jigsaw
Registry Entry made by Jigsaw
You CAN Decrypt and Remove Jigsaw Ransomware!
- To decrypt your files, you will first need to stop the running processes used by Jigsaw in Task Manager, firefox.exe and drbx.exe. This will prevent Jigsaw from further encrypting files on your computer.
- Next, you will need to run MSCONFIG.exe and disable the firefox.exe startup entry which points to the %UserProfile%\AppData\Roaming\Frfx\Firefox.exe executable.
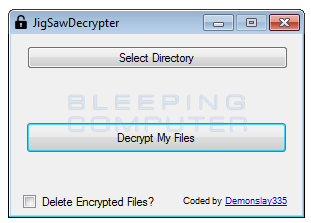
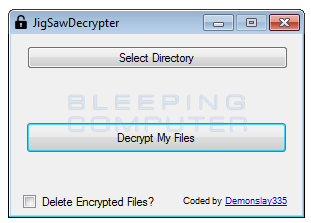
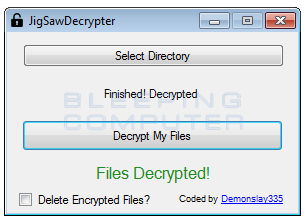
- Download and extract JigSawDecrypter.
- Run JigSawDecrypter.exe.
- Click Select Directory to choose the infected directory.
- Click the Decrypt My Files (DO NOT check Delete Encrypted Files? Until after you have verified the files were successfully decrypted!)
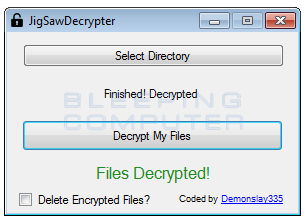
- After the software has decrypted your files, you will see this window.
Special Thanks to MalwareHunterTeam and BleepingComputer for publishing and sharing JigSawDecrypter.
When Failure to Act Results in a Compromised Network – A Sad Cryptolocker Tale
Why I'm breaking up with my antivirus software.
How to Stop Ransomware Attacks
There are a number of things you can do today to prevent malicious software like banking Trojans and ransomware from entering your network.
Employee Education - Have frequent reviews with employees discussing the threat of phishing attempts and what to look for in emails to avoid getting compromised.
Run nightly backups - Backups won’t save you from all the hassles of banking Trojans but can be useful to restore data from a ransomware attack.
Advanced Endpoint Protection – Use to detect suspicious behavior that signature-based solutions miss.
Deploy WatchPoints: "WatchPoints" are files placed on your network to lure attackers who have breached your defenses. For example, one WatchPoint offered is a Microsoft Word document that alerts you when it is accessed. The idea is to give it a very attractive title like “Sensitive Passwords.docx” to tempt the cybercriminals. If the document is retrieved, you and the WatchPoint team automatically receive a notification.
Contact us to see how a simple WatchPoint sensor disguised as a Microsoft Word file works. When someone opens the document, you will get an email alert.
More Articles for Your Enjoyment!
Why Didn't My AntiVirus Detect CryptoWall?
Another Hospital Becomes Victim of Ransomware
Banking Trojan Targeting Android Devices Can Bypass 2FA
Why Closing Unused Server Ports is Critical to Cyber Security